The new ServiceNow release takes us to the Japanese capital – Tokyo. There is a famous saying “If you look at history, innovation doesn’t come just from giving people incentives; it comes from creating environments where their ideas can connect.“ In every release, ServiceNow is coming up with new innovations and upgrades to effectively implement solutions for its customers. In Tokyo, Security Operations (SecOps) came across new ingenious workflows and processes to respond to threats faster & more efficiently, and view the organisation’s security posture.
Security Incident Response
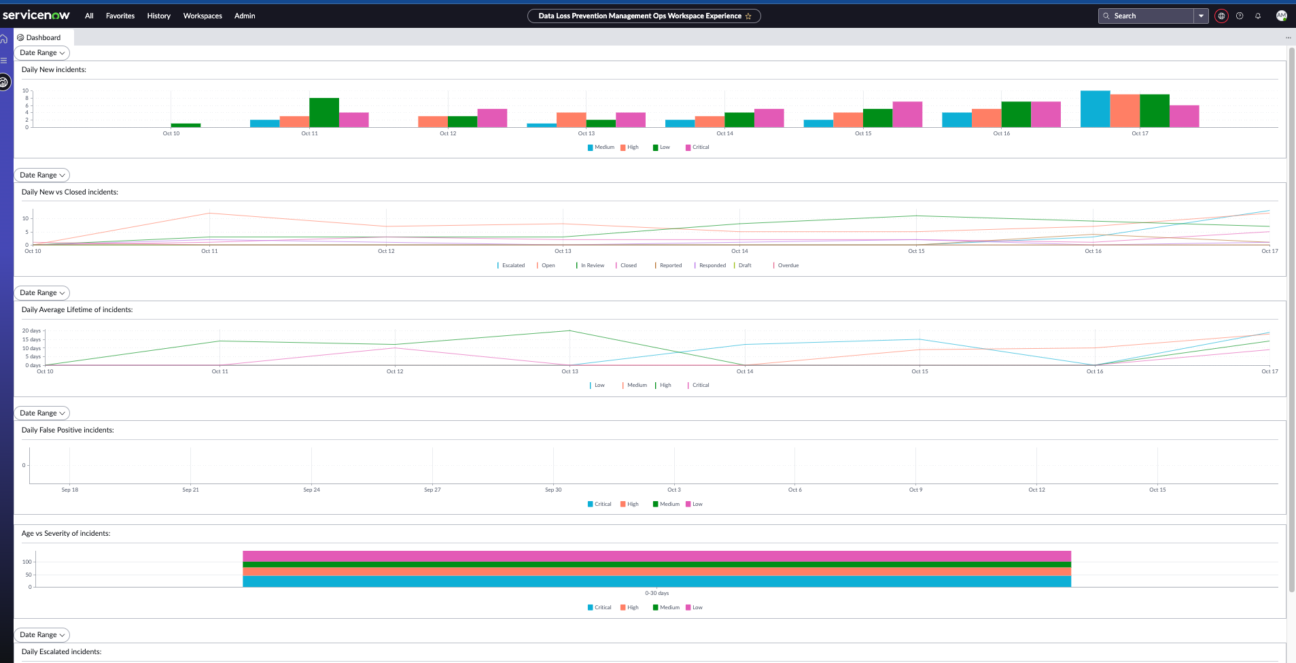
Data Loss Prevention (DLP) Integrations
Undoubtedly, these days data loss prevention is one of the most important practices in the majority of organisations. So, what is the best way to protect it? With the Data Loss Prevention (DLP) application. Thanks to this tool, you can manage your clients’ important and sensitive information, e.g. financial and proprietary data, health records and social security numbers. Additionally, all of this can be automated using remediation workflows.
There are plenty of updates in the Tokyo release related to Data Loss Prevention. One of them gives you the ability to proactively inspect, analyse, and contain known or unknown threats at any endpoint by using the Microsoft Defender for Endpoint integration. It also helps with:
- creating configurations to retrieve details such as hosts, logged-in users, related machines and other capabilities related to enrichment,
- creating requests to isolate any endpoint or machine from accessing the network and remove that from isolation.
Integrations within DLP, such as Proofpoint and Netskope, can also help to filter DLP incidents and import them to the Now Platform. There, both incident and notes based on actions performed on the incidents, are updated. Lastly, there is also an API integration with Symantec, allowing organisations to import incidents related to DLP for endpoint, network, email etc. straight into the Now Platform.
Vulnerability Response
When we look at the Vulnerability Response application, there are quite a lot of new enhancements in the Tokyo release. Let’s have a look at the most crucial ones one by one.
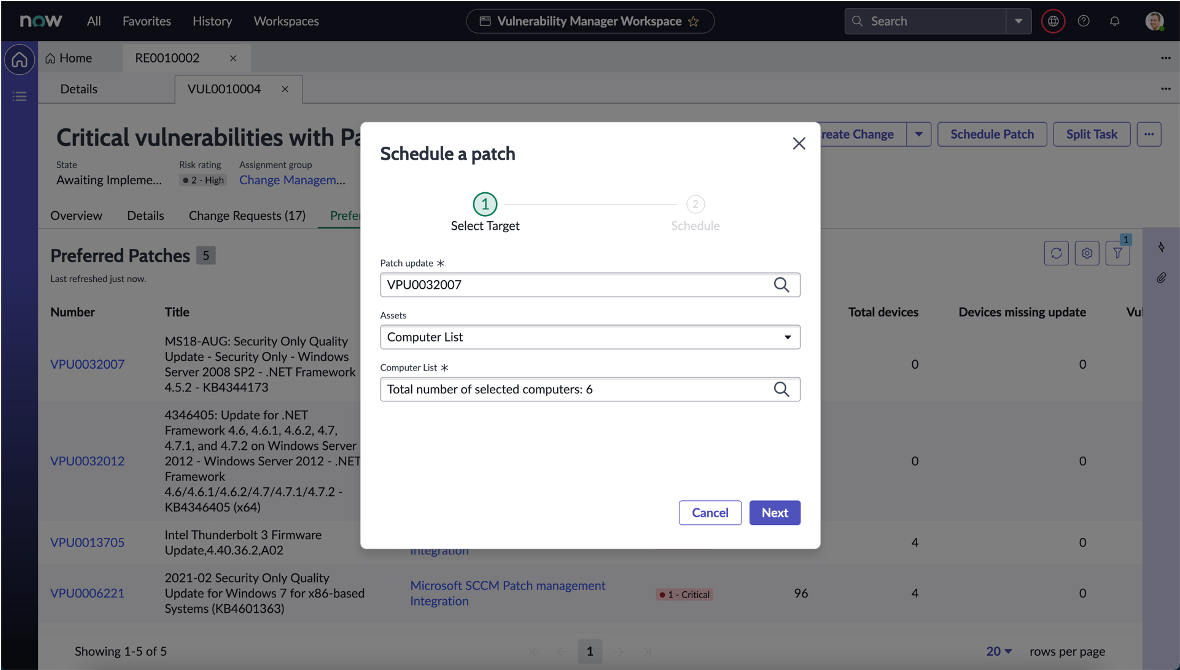
Patch Orchestration for Vulnerability Response
Together with the ServiceNow Tokyo release came new functionality that was requested for a long time by many customers – Automated Patch Orchestration.
As part of the Vulnerability Response workflow, you can now schedule patches with Microsoft SCCM and also HCL Big Fix. All as a part of the Vulnerability Response process – closing the full loop in Vulnerability Management. This integration will reduce the time and effort for Remediation owners, allowing them to meet the SLAs more efficiently. Previously, security and IT teams had to use multiple systems or interfaces to schedule the patches and fix the vulnerabilities. Now, everything will be done straight from the ServiceNow platform.
Please note that for the licensing implications, this application requires a VR Enterprise license.
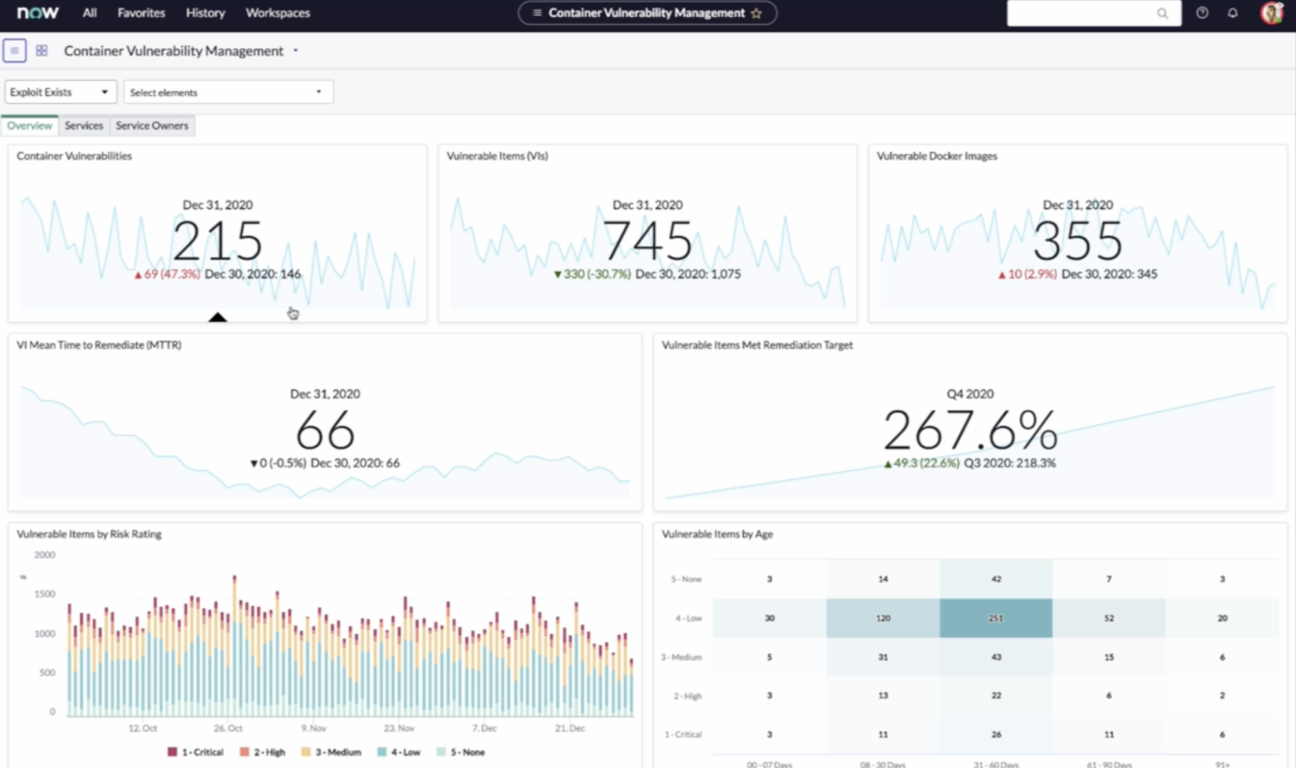
Container Vulnerability Response
Container Vulnerability Integration is part of the ServiceNow “Cloud Security” story.
As organizations are moving to the cloud, they are starting to adopt & adapt the platforms like containers to handle the workload. This presents a challenge within the vulnerability response because the assets are not easy to pin down and it is hard to apply the classic vulnerability approach.
This new feature allows us to connect and pull container information to quickly address and remediate those critical vulnerabilities in container images. Additionally, it helps to reduce the risk of dynamic cloud deployments and container vulnerabilities.
As with all Cloud Security applications, these features come as a part of the VR Enterprise license.
Vulnerability Response Integration with CISA
Just like the previously described features, Vulnerability Response Integration with Cybersecurity and Infrastructure Security Agency (CISA) was also highly requested by customers.
This particular integration, allows you to extract information from CISA about known exploited vulnerabilities (KEV) catalogue and map to CVEs. It helps to identify and prioritise which vulnerabilities to patch first and reduce the risk faster.
It comes with the VR Standard license.
—–
Do you have any questions regarding SecOps? Do not hesitate to contact us to receive the most recent information regarding ServiceNow and its products. Feel free to reach out if you are interested in a demo or professional services.

Certified ServiceNow Experts at your service
ServiceNow can empower your employees and clients with digitalized workflows, and Devoteam, as the #1 preferred Partner in the EMEA, is eager and ready to help make your digital transformation journey a success. Ready to see what we can bring to the table?